Physical perimeter security
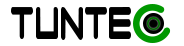
From the outset, the notion of security perimeter allows us to get to the heart of the matter. Within this scope, the company must delay or prevent physical access to premises, systems and information by unauthorized actors. The constraint is noticeable and it is therefore not a question of forgetting to maintain the availability of access for legitimate actors!
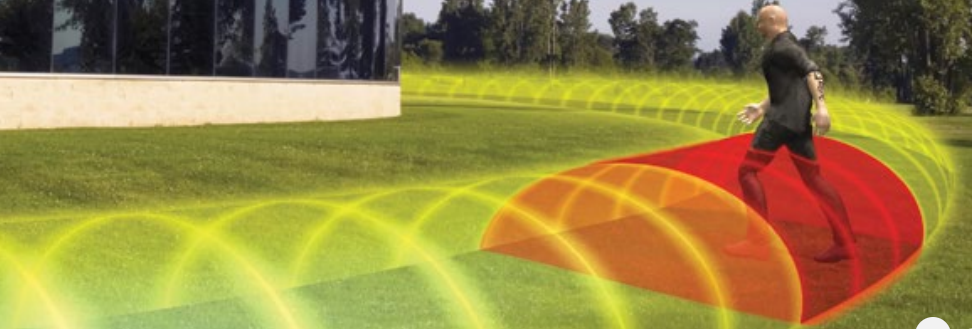
The security perimeters will in particular allow you to define sensitive areas containing your vital systems. The protection of physical access must be sufficient to respond to the threat scenarios identified.
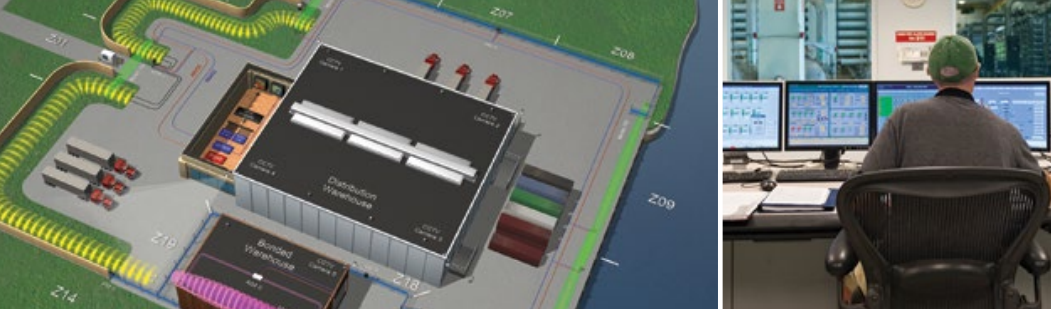
Securing an entrance also means controlling the physical access of people and equipment to the different zones (depending on the sensitivity of these zones). It is a matter of supervising human activity since no passage should be transparent.
OUR MISSION
Provide industry-leading system design resources, unprecedented technology options with flexible networking capabilities, and the best customer support tools to deliver reliable, long-term solutions to all issues perimeter protection to all our customers around the world.
TUNTEC offers its customers the most complete range available in terms of electronic systems for detecting perimeter intrusions (unauthorized access, risks of vandalism, theft or malicious attack on critical infrastructures and threats to people). We ensure that all critical elements inside and on the detection perimeter are protected by reliable technologies that give the best results in the industry.